Do you know what the greatest threat to your computer network is? It’s your employees.
Meanwhile, cybercriminals are getting more sophisticated, making scams and phishing attacks more difficult to detect than ever.
As a result, nearly 9 out of 10 data breaches are caused by human error.
How do you stop employees from endangering your business when they click on things that they shouldn’t?
At EZComputer Solutions, our team recommends implementing a powerful but affordable tool called ThreatLocker.
What is ThreatLocker?
ThreatLocker is a zero-trust security tool that stops users from installing or running malicious software on your computers. It includes:
- Application Whitelisting–gives your business complete control over what programs are allowed to run and blocks everything else
- Ringfencing–stops attackers from misusing trusted software by controlling how programs are allowed to interact with each other, your data, and your network
- Storage Control–monitors and controls file access to protect your data from being manipulated when it shouldn’t be
ThreatLocker will protect your network against malware threats, data theft, and remote access attacks. It even goes beyond the protection your antivirus software can offer by protecting against malware embedded in trusted programs like Office and new threats that haven’t been discovered yet.
Why antivirus is not enough
While you should absolutely have a good antivirus solution, antivirus alone is not enough to protect your business.
Traditional antivirus software looks for threats based on known suspicious behaviors. It only stops viruses IF it correctly identifies them as threats.
The problem is that because it relies on patterns and rules established by previous threats, traditional antivirus software may not catch new variations of viruses and malware.
Meanwhile, cybercriminals are creating new malware variants at an alarming rate–making it nearly impossible for your antivirus to keep up. In 2019, there were 144.91 million new malware variants that were undetected by traditional antivirus software.
Zero-trust security software like ThreatLocker takes the opposite approach, which is “never trust, always verify.” Rather than trying to identify individual threats, ThreatLocker only allows trusted software to run on your computers, and it blocks everything else.
| Traditional Antivirus | ThreatLocker |
|---|---|
| Allows access by default | Denies access by default |
| Protects from known threats | Blocks and verifies any unknown software |
| “ANYTHING can run UNLESS it’s a threat” | “NOTHING can run UNLESS it’s trusted” |
How Does ThreatLocker Work?
Using a combination of application whitelisting, ringfencing, and storage controls, ThreatLocker protects your business from malicious software and cybersecurity threats caused by human error. Here’s how it works:
Step 1: Learning Stage
Before blocking anything, ThreatLocker does a complete audit of your network to learn what files and programs each user uses regularly. From there, we use that audit to build security policies that make sense for your business, such as:
- Which programs should be trusted (ex. Office, Chrome, Zoom, Slack, etc.)
- Who has access to certain files or programs (ex. Only accounting personnel have access to Quickbooks)
- Where you can access certain files or programs (ex. Remote employees can’t access sensitive data from their home or personal devices)
The learning stage typically takes about 2 weeks to complete.
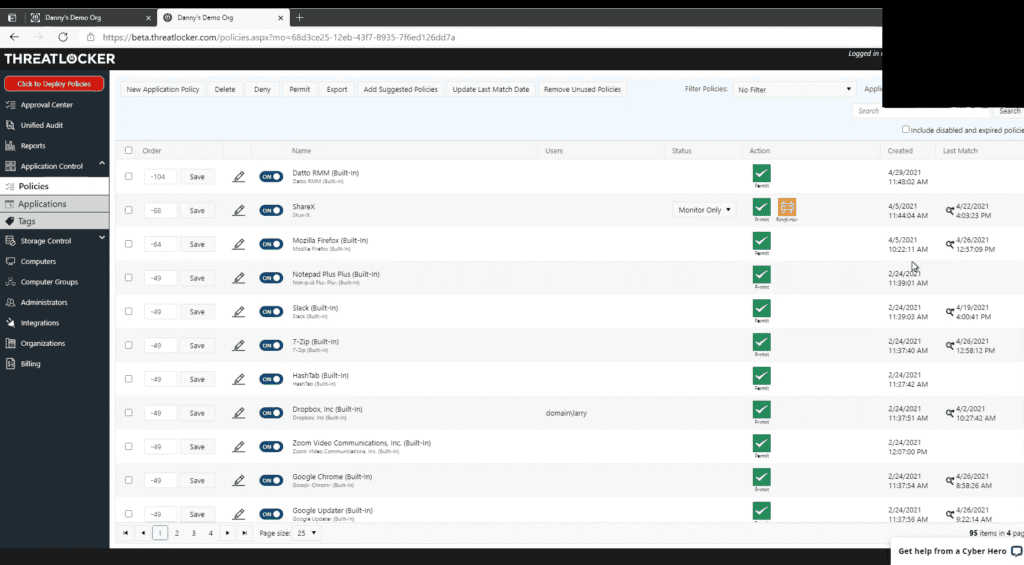
Step 2: Turn on Protections
Once the audit is complete and we have your customized security policies in place, we turn on ThreatLocker’s protections. From this point on, your computers are secured, and ThreatLocker will block any unauthorized program from running.
This means that if an employee clicks on a link in a phishing email and it tries to install a malicious program, ThreatLocker will prevent the program from installing and alert both the user and the IT administrator.
ThreatLocker even protects against malware that piggybacks off trusted programs, like Office. We set up security policies that essentially ask, “What does Office actually need to do?” and ThreatLocker prevents Office from doing or accessing more than it should be.
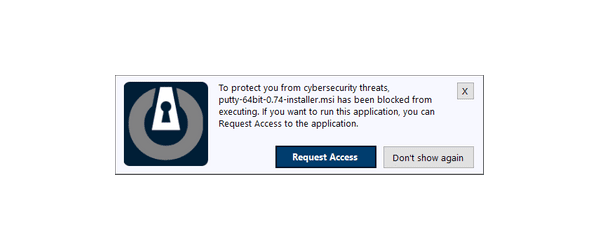
Step 3: Request Access
Any time you click on something that isn’t allowed by ThreatLocker, you’ll get a notification message that the program has been blocked. If it’s legitimate, they can request access, and we can review and grant access immediately.
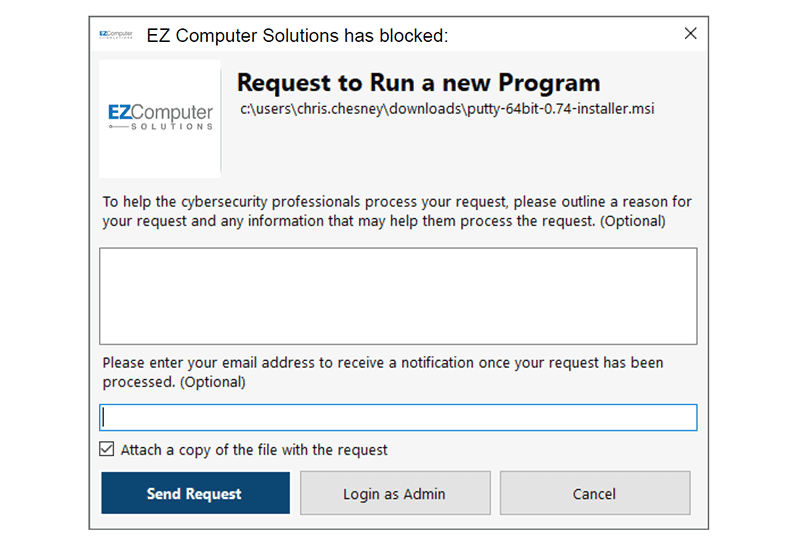
While it may seem like a pain, requesting access does two critical things: 1) it prevents employees from overriding a warning and installing something malicious, and 2) it ensures there’s a second set of eyes on any programs that could be a threat to your network.
Once we verify that a program is safe, we can approve a program in about 30 seconds and update your security policies so ThreatLocker allows that program in the future.
Protect Your Business Against Human Error with ThreatLocker
ThreatLocker puts your business in control of what is running on your computers, rather than leaving that control in the hands of individual employees, or the hackers! Protect your business from threats that your employees inadvertently introduce and your antivirus software won’t catch.
Our team at EZComputer Solutions will make it fast and easy to get set up with ThreatLocker’s powerful anti-threat security. Contact us today to get started!